 This is the second installment of a three-part blog series where CSC® explores how the WHOIS database has become a window into the security set up of an organization due to the ever-increasing threats of cyber crime. Click here to find out the #1 threat to domain security in last week’s post.
This is the second installment of a three-part blog series where CSC® explores how the WHOIS database has become a window into the security set up of an organization due to the ever-increasing threats of cyber crime. Click here to find out the #1 threat to domain security in last week’s post.
#2 threat: provider quality
The WHOIS, in many cases, will list the domain name registrar and the domain name system (DNS) servers. Not all registrars and DNS providers are equally secure with the infrastructure and processes in place to withstand attacks, which leaves WHOIS information available for bad actors to target brands with a weak setup. Comparison shopping is key to ascertaining the kind of security each registrar offers versus what your brand needs.
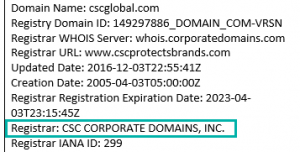 Registrar
Registrar
It’s well documented1 that retail registrars are seemingly less secure, and therefore are targeted and compromised more frequently than corporate registrars. Companies should partner with a registrar that has invested heavily in security at the technology level, within the training of staff, and within the values of the company. Ask these questions of a potential registrar. Doing the research in advance of signing with a provider helps a brand avoid issues down the line.
DNS provider
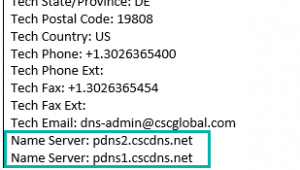 The investment required to build a robust, in-house, enterprise-level DNS infrastructure capable of enduring today’s cyber attacks means most companies should choose to outsource to a specialist provider.
The investment required to build a robust, in-house, enterprise-level DNS infrastructure capable of enduring today’s cyber attacks means most companies should choose to outsource to a specialist provider.
To run your own DNS, our estimates show that it’s going to be a costly option:
- Staff x 2 for holiday and sick days = $150K/year
- Hardware and bandwidth from ISP = $40K/year
- Open source DNS software such as BIND = known security risks. And the most recent zero day vulnerability2 was only last year. This had a massive impact on many DNS providers and companies.
Not only is it expensive for a company to run its own DNS, but the estimated average annual cost to businesses from distributed denial of services attacks is $3.5 million3. Given that the average cost to outsource DNS is a fraction in comparison should be a compelling reason to find a secure enterprise-level DNS provider.
CSC’s research suggest that 22% of organizations still operate their own DNS, and experience tells us many simply do not believe that they will be a target. This is misguided given that we have seen a vast range of companies and services in many different industries succumb to DDoS attacks.
In the news:
- Small businesses attacking competitors
- Hotels held to ransom
- Global banks being targeted by hacktivists
- Universities DDoSed by the Internet of Things
- Governments forced offline
Finally, what is clear from recent events4 is that not all enterprise-level DNS providers are born equal, and therefore, although you might be offered 100% uptime, you should carefully check the track record of any provider before signing on.
Brand owners should ensure that security considerations are top of their list when reviewing and choosing suppliers or considering managing a service in-house.
Considerations should include:
- Ability to meet scope of needs within budget
- Security culture and ongoing training
- Track record and reputation
At CSC, we carefully chose our partners for DNS and secure sockets layer certificates based on these criteria. If you have a concern regarding the management of any of your digital assets, CSC would be happy to provide a complimentary security audit.
Next week, we wrap up our blog series with the #3 to domain security.
Domain Security, Part 1: Do You Know Who’s in Your WHOIS?
Domain Security, Part 3: Preventing Unauthorized Access
1Various articles on past compromises: http://www.pcworld.com/article/2892632/driveby-attack-relies-on-hacked-godaddy-accounts.html, http://thehackernews.com/2015/01/godaddy-vulnerability-allows-domain_20.html, and https://betanews.com/2016/08/26/godaddy-phishing-scam/
2http://news.softpedia.com/news/attackers-use-recent-bind-flaw-to-attack-dns-servers-509315.shtml
3https://security.radware.com/uploadedFiles/Resources_and_Content/Attack_Tools/CyberSecurityontheOffense.pdf
4Recent attacks: https://www.theguardian.com/technology/2016/oct/26/ddos-attack-dyn-mirai-botnet or https://www.scmagazineuk.com/ovh-suffers-11tbps-ddos-attack/article/532197/