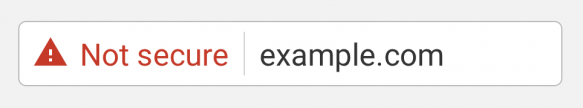
 Google has long championed a more secure internet, and their next move will now take those efforts to a new level. With the release of Chrome 68 in July 2018, Google will mark any site without an SSL certificate (non-HTTPS) as “not secure.”[1] This will be enforced regardless of content or the intended use of the site, and highlights the importance of encryption and data security online.
Google has long championed a more secure internet, and their next move will now take those efforts to a new level. With the release of Chrome 68 in July 2018, Google will mark any site without an SSL certificate (non-HTTPS) as “not secure.”[1] This will be enforced regardless of content or the intended use of the site, and highlights the importance of encryption and data security online.
At the start of 2017, any website collecting login or payment information—which the vast majority of companies already had secured—required encryption or would otherwise be forced to alert its visitors that it was “not secure.” This was followed by the distrust of any site where a visitor could input information, including search boxes.
From July this year, all websites without HTTPs will be marked as not secure, even if your site does not collect user input– this will cover any site that is live, or visible to external users.
Google’s advocacy for internet security extends to their treatment of Certificate Authorities whose validation processes were deemed substandard.
In 2017, Google also announced its plan to progressively distrust Symantec certificates, which led to DigiCert’s acquisition of Symantec. This began with the distrust of all Symantec family certificates issued before June 2016, and is to be followed by a second phase in September this year, impacting all Symantec certificates issued between June 2016 and December 2017.
At CSC, we recommend all clients fully account for their SSL certificates; according to the Ponemon Institute, 51% of Global 2000® companies have not done this. An expired SSL or distrusted site can mean lost revenue and damage to brand reputation.
Therefore, asking the right questions is pertinent: Are you aware of all the certificates your organization owns? Are you receiving renewal reminders? Do you have a mitigation plan for impacted distrusted certificates?
It is important to review your domain portfolio, to look at where your sites are not protected with SSL, as well as where they are located, and which certificates have different validation levels to cover your needs.
Contact us to discuss how we can help.
[1] https://security.googleblog.com/2018/02/a-secure-web-is-here-to-stay.html